The ASD Top Four, if you have not heard of them, have become part of the highly popularised Essential Eight.
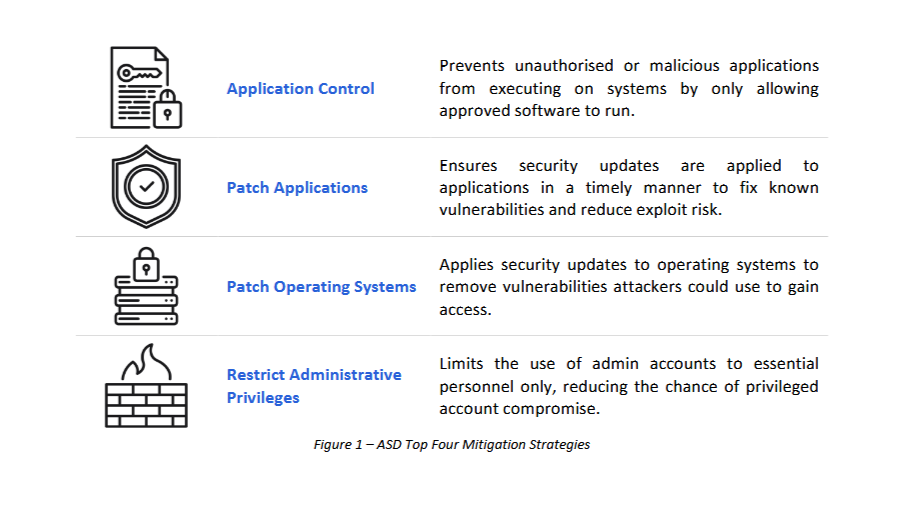
Back in 2015, the ACSC produced a threat report, and among the buzzwords it included a handy statistic: the Top Four were able to prevent and mitigate at least 85% of targeted cybercrime intrusions responded to by the ASD.
But how do they fare now? They are still great, because they are in the current recommendation from the ASD. Yet can they still boast that 85% rate in today's world? I will wager the answer is no.
That is not to discredit the four mitigation strategies, more to say they are an exceptional start to a cyber security strategy, and with some minor additions you could sleep better at night.
When thinking about including real-world evidence in this article, the internet provided me with a helpful dose of analysis paralysis up until reading a rather unfortunate incident over in Canada.
Why it is worth the investment
You may have caught the headlines “Cyber insurer denies $18 million claim&rdquo which makes you wonder what heinous crime this organisation did to have their claim rejected... they did not have MFA.
One article reads.
The Canadian city of Hamilton, Ontario fell victim to a ransomware attack in February 2024. This attack was similar to countless others where initial access was gained via an externally-facing machine with weak credentials, which then lead to internal infrastructure being encrypted and a ransom for the decryption binaries being posted.
From the Australian parliament's cyber security compliance report (2017): the ASD says implementing the Essential Eight “can save organisations considerable time, money, effort and reputational damage compared to cleaning up after a compromise” and considers them the cyber security baseline for all organisations.
Which seems ever more apparent with that article and the many others like it.
That helps reinforce why the Essential Eight is so highly regarded.
So, what are the additions?
In today's age of cloud everywhere with identity management, SaaS applications and email, the Top Four do not protect those surfaces. The data they hold is not protected by the Top Four alone.
Instead of saying “just add one of the Essential Eight controls,” it felt more useful to highlight business email compromise.
The ASD provides quality guidance: phishing and awareness training, multi-factor authentication, strong passphrases.
Not groundbreaking, but they would have changed the headlines. Two are easy enough, and phishing and awareness training is often overlooked because products are expensive or material is dated.
If you are interested, there is an Australian team doing it right at Phriendly Phishing.
From the Top Four to the Complementary Five and a bit
Without taking away from the Essential Eight, full implementation cost means not everyone will land all eight at once and it should not feel like boiling the ocean.
Small steps toward the Essential Eight always pay dividends or $18 million, to be exact.
